Trusted Platform Module (TPM): Enhancing Digital Security and Beyond
In an era where digital threats and cybersecurity breaches are becoming increasingly sophisticated, the need for robust and comprehensive security measures is paramount. Trusted Platform Module (TPM) has emerged as a pivotal technology that contributes to elevating digital security to new heights. In this article, we will delve into the concept of TPM, its applications across various operating systems and applications, and explore the different versions available.
Understanding Trusted Platform Module (TPM)
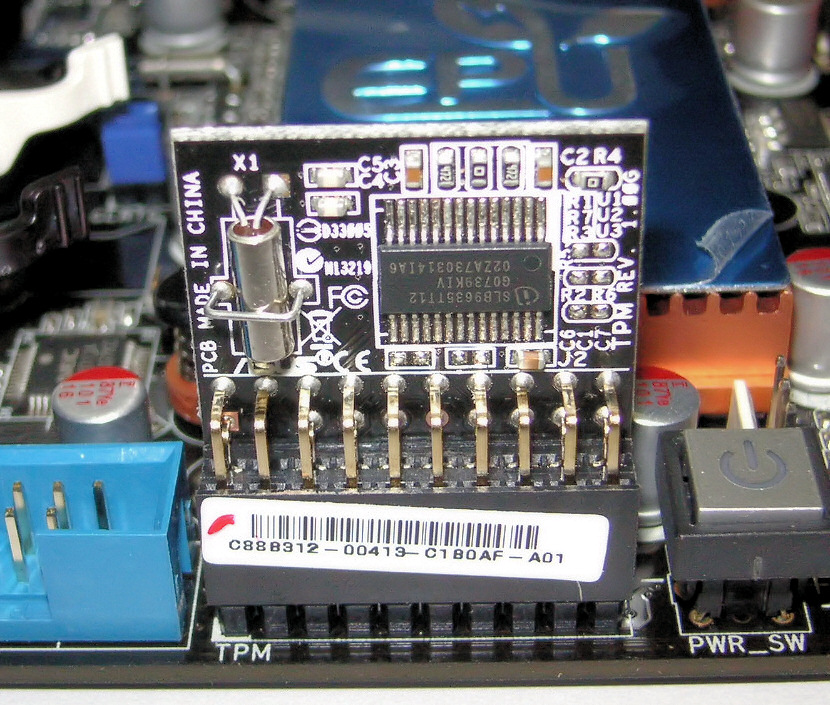
At its core, Trusted Platform Module (TPM) is a specialized hardware-based security chip that is designed to ensure the integrity, security, and authenticity of various digital processes. It is integrated directly into a computer’s motherboard or other hardware components and functions as a secure cryptoprocessor. TPM generates and stores cryptographic keys and provides a secure environment for sensitive operations like encryption, decryption, and authentication.
One of the key features of TPM is its ability to securely store encryption keys, passwords, and digital certificates away from the main CPU and memory. This prevents malicious software or attackers from gaining unauthorized access to sensitive data. TPM also supports secure boot processes, which ensure that only trusted software components are allowed to execute during the system startup.
Applications and Operating Systems Requiring TPM
The applications of Trusted Platform Module span across a wide array of scenarios, with the primary goal of reinforcing security and trust in digital operations. Some of the key areas where TPM is employed include:
- Full Disk Encryption: TPM is often used to store encryption keys for whole-disk encryption solutions. This ensures that even if an unauthorized user gains access to the physical storage, the data remains unreadable without the correct key stored securely within the TPM.
- Secure Boot and System Integrity: TPM is instrumental in enabling secure boot processes. It ensures that the system boots only into trusted software components, preventing the execution of malicious code during startup.
- Digital Signatures and Authentication: TPM can be used to generate and store digital certificates and keys for signing documents and authenticating users or devices, contributing to secure communication and identity verification.
- Virtualization Security: TPM can enhance security in virtualized environments by providing hardware-based isolation and secure key storage for virtual machines.
- Password Protection and Management: TPM can help in managing and protecting passwords and other authentication credentials, reducing the risk of credential theft.
Versions of Trusted Platform Module
Trusted Platform Module technology has evolved over the years, leading to the development of different versions with enhanced features and security capabilities. As of my knowledge cutoff date in September 2021, the following versions of TPM were available:
- TPM 1.2: This was one of the earlier versions of TPM, offering basic security features such as secure key storage and basic cryptographic operations.
- TPM 2.0: This is the current widely adopted version. TPM 2.0 introduces advanced cryptographic algorithms, enhanced key management, improved secure boot mechanisms, and more comprehensive support for various security applications.
Conclusion
In an increasingly digital world where data breaches and cyberattacks are rampant, technologies like Trusted Platform Module play a pivotal role in fortifying digital security. By providing a dedicated hardware-based security chip that can securely store keys, authenticate devices, and ensure the integrity of critical processes, TPM enhances the trustworthiness of computing systems. Its applications span across encryption, authentication, secure boot, and more, making it a crucial component in safeguarding sensitive data and digital operations. As technology continues to evolve, the evolution of TPM versions underscores its enduring relevance in the realm of cybersecurity.
Listings related to article "Trusted Platform Module (TPM): Enhancing Digital Security and Beyond"
Top-Rated Computer and Mac Repair Services in Miami
Looking for reliable computer and Mac repair services in Miami? Our experienced technicians offer quick, professional solutions for all kinds of devices—including laptops, desktops, iMacs, MacBooks, and more. Whether you’re facing hardware failures, software glitches, system crashes, or need an upgrade, we’re here to help.
- Category
- Computers » Hardware » Support and Services
UPI Chalega
UPI, or Unified Payments Interface, serves as a digital payment solution enabling the effortless transfer of funds between bank accounts via mobile phones.
- Category
- Business » Financial Services » Banking Services
Hackaday
A community-driven platform showcasing creative and often unconventional projects related to electronics, hardware hacking, and DIY technology.
- Category
- Computers » Hardware » Do-It-Yourself
More articles like "Trusted Platform Module (TPM): Enhancing Digital Security and Beyond"
From Silicon to Software: How Computers Became the Engine of Modern Life
Computers are programmable machines that process data into useful results, powering everything from personal creativity to global infrastructure. This article explains how computers work, their main types, core components, and what’s next for computing.
Inside the Machine: How Computers Turn Ideas into Action
Computers are versatile systems that process data, run software, and connect people and services worldwide. This article explains how they work, what they’re made of, and how to choose and use them wisely.
From Silicon to Society: How Computers Power the Modern World
Computers are programmable machines that process data to perform tasks ranging from simple calculations to complex simulations. This article explains how computers work, the major types, key components, and why they matter in everyday life.